The Coronavirus and Small Business Law Series
This blog post series provides key legal strategies, practices, and policies to help you secure your business success during the Coronavirus pandemic.
With this knowledge, you can return to what you do best – your service or product.
In the first of this series, I discussed key intellectual property practices to protect your uniqueness.
In this second post, I’ll cover personal device usage, or more commonly known as Bring Your Own Device (“BYOD”) .
Topic #2: Bring Your Own Device Solutions

KEY BRING YOUR OWN DEVICE STRATEGIES
At the present time, as cities across the United States tighten quarantine to slow the spread of the coronavirus pandemic, businesses are turning to remote working arrangements.
However, a recent survey, prior to the coronavirus pandemic, found that nearly 40% of full time workers in the United States worked solely on-site. 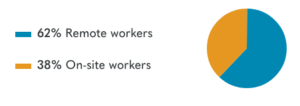
source: https://www.owllabs.com/state-of-remote-work/2019
Is your business part of that 40%? Do you allow your employees to use their personal electronic devices to make work calls, and/or send and receive work emails? Are your suddenly work-from home employees using their own cell phones, tablets, and laptops?
If you answered yes to any of these questions, then you need to have and communicate BYOD practices and policies.
KEY BRING YOUR OWN DEVICE PRACTICES

Generally speaking, establishing security protocols is especially important with remote workers.
Therefore, put data protection practices in place now. Without delay, require strong passwords and automatic locking after periods of inactivity. Also, establish protocols for reporting lost or stolen electronic devices. Further, mandate antivirus and protective software. Additionally, require regular backups.
At the present time, you should consider implementing mobile device management technology. This creates a virtual partition in each device thereby separating work data from personal data. The partition facilitates security measures while limiting the company’s access to only work data.
Although typically controversial, protect company data and information by providing your employees with an electronic agent on their personal devices to enforce security configurations.
KEY BRING YOUR OWN DEVICE POLICIES

A Bring Your Own Device Policy establishes the rules and conditions for use of a privately-owned electronic devices. Generally speaking, this includes work for and on behalf of your company; or to access, either locally or remotely, computer networks and data owned by your company.
These rules and conditions help ensure appropriate protection of company and customer information when stored on a privately-owned device and/or accessed through the device.
Your Bring Your Own Device Policy should apply to information in all forms used by, for, and within the Company.
Business information examples:
- Correspondence (including e-mail, text messages, and instant messages)
- Reports
- Documents
- Presentations
- Manuals
- Customer policies
- Electronic or printed information
- Voicemail
Employee Responsibilities
Your company policy should obligate your employees to protect the security, confidentiality, and integrity of the company’s information.
Some key employee responsibilities:
- Prevent other users from accessing Company information.
- Use personal devices in compliance with all applicable Company Policies while conducting Company business.
- Use personal devices for business purposes in a lawful and safe manner.
- Notify the Company immediately if a personal device is lost or stolen
- Notify the Company immediately if any unauthorized third party intrusion.
- Maintain a strong password on personal devices at all times.
Implement these BYOD strategies, practices, and policies today to secure your business success.
Do you need help implementing Bring Your Own Device strategies, practices, and policies? I can help. Contact me here.

leave a comment on this post.